I am in urgent help of getting rid of this Win32/RBrute.A virus. I did run MalwareBytes for several times and it did help me remove some viruses but when it comes to this stubborn Trojan which I have had on my laptop for a couple of days it does not seem that powerful. Though it says it has removed the virus but I still get annoying pop-up message of infection after the reboot. I’ve heard that this virus can steal my personal information. What will it do if I cannot remove it? What should be done to delete it?
Win32/RBrute.A Trojan Virus Details
Win32/RBrute.A is a threat to computers which has been reported by lots of net users all over the world. The particular pop up of this virus infection is always classified as a Trojan virus. It has been caught by some different antivirus software. No one wants to have such virus on one’s computers because of the bad characters and potential risks of the virus. It can make the system in low protection and lead it to poor performance. It is well-designed and is enabled to sneak into random systems around the world from the internet. The installation of the virus and its sponsored programs do not require any permission of the computer users. Basically speaking, net users cannot even know when and how they get infected. It is a very important task to do a complete clearance of the virus in order to prevent potential damages from happening on the infected computers. Victims will suffer more and more computer problems after the virus arrives on the system. The internet connection may not work properly. There may be some unwanted changes on desktop icons and background images too.
Note: Manual Removal requires expertise and it is for advanced users, if you don’t have much experience in dealing with redirect virus.
Contact YooSecurity Online PC Experts for removal assistance.

Symptoms of Similar Trojan Infection :
– This virus can escape from most antivirus protection and get itself installed on computers especially with Windows operating systems.
– It can cause constant stuck or even blue screens on the infected computers.
– Computer users will experience constant security pop ups on the computers which may not truly represent the status of the PCs.
– Certain malware or spyware may be prompted by these fake security pop ups which will end up scamming money.
– Sensitive data like privacy can also be stolen and taken advantages by cyber criminals.
Manual Removal Step by Step Instructions
Up till now, there is not a perfect antivirus that can detect this pesky Trojan virus or delete it completely. Win32/RBrute.A has been updated by remote and backstage cyber criminals and is able to escape from the scan of any anti-virus programs thus it is hard to be removed or even found. The most effective way is to remove it manually. The following instructions need quite level of computer expertise. If you don’t know how to that correctly, please contact with YooSecurity online support now!
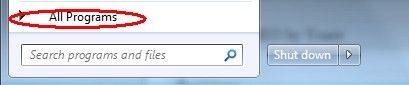
Step A: Check on your start menu if there are any programs that you are not familiar with. The strange ones will often related to the virus process as it can start automatically with the windows. You can press on Windows key or just click on the start menu to view it. Please notice that you need to click on All Programs to have an overall check on it.
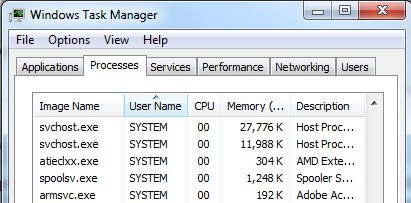
Step B: To remove the Trojan the first thing we need to do is to end its process thus we will not get the error message when we delete its files. To do that, open Windows Task Manager to end process related to this Trojan infection. You can press Ctrl+Alt+Del keys at the same time to pull up Window Task Manager; go to Processes tab on top and scroll down the list to find.
Step C: Always any virus files will be hidden files. So we need to show hidden files before we are going to delete them. Open Control Panel from Start menu and search for Folder Options (As an easy way you can open a folder and hold Alt key and tap on T, O key one by one and folder option window will pops up). Go to Folder Options window, under View tab, tick Show hidden files and folders and non-tick Hide protected operating system files (Recommended) and then click Apply and then hit OK.
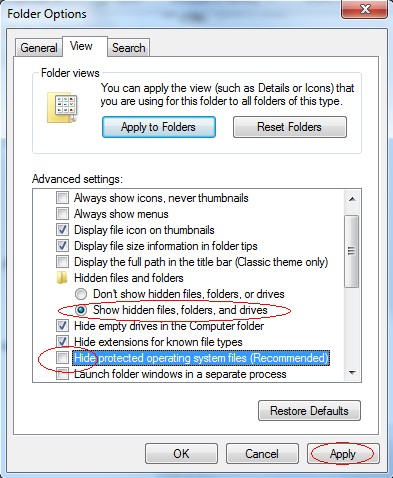
After we can see hidden folders and files we can go to system files and delete the infected files. The path of the virus often can be found from the antivirus which detects it.
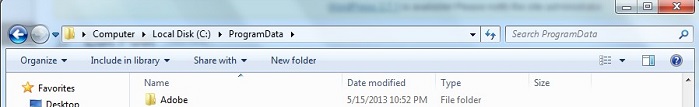
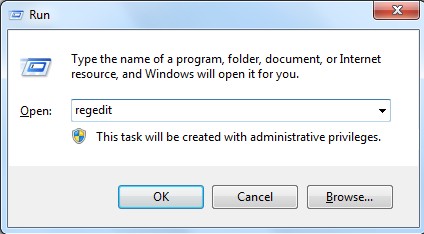
Step D: After we delete the virus files from system data we get to remove the registry of the virus from registry editor to prevent it from coming back. You can get Registry Editor by pressing Windows+R keys to pull up Run box and type in regedit to open Registry Editor.
The following is how Windows Registry Editor looks like.
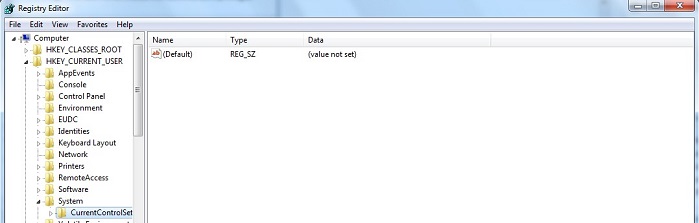
Step E: Delete all these associated files and registry entries with this Trojan virus from Registry Editor. The registry files are listed randomly. Besides, you need to delete the infection files of the redirect virus from your system files to prevent it from coming back. Those files are named randomly also but may be different on different operating systems.
Video on How to Modify or Change Windows Registry Safely:
Summary:
Apart from the fact that the PC runs rather slower than it ever does, computer users can also be confronted with weird things such as having unauthorized programs popped up and constantly being redirected while online to unwanted places. All those can be caused by the virus infection. Among the effects of the virus, privacy security issue ranks at the top of all as the virus can help cyber criminals steal confidential information from infected computers. If you do not want any of these happen to you, a complete virus removal should be achieved ASAP via manual removal process. If the infection is not cleared out there will be possibility for remote hacker or third party to get remote access to the vulnerable system. Your privacy and security will be in danger.
Note: Have tried many methods but failed to get rid of this Trojan virus? If you have no clue, please contact YooSecurity Online Experts in time to save your computer.
Published by Tony Shepherd & last updated on April 4, 2014 1:30 pm










Leave a Reply
You must be logged in to post a comment.