How to remove Win32/bitcoinminer.AF form windows operating system? I have got this Trojan several days ago and my antivirus warns me that I have this infection. I clicked on the option to delete it but I failed to remove the virus. Because I still get the alert of the infection after I restarted my computer. There seem to be many places where the infective files are. But the antivirus cannot find them all or it cannot delete them completely. That might be the reason why it kept coming back after a reboot. What method can I have a try?
Computer Infected with Win32/bitcoinminer.AF–How to Remove?
Win32/bitcoinminer.AF is a recently released computer infection. It is generally categorized as a Trojan virus issue and takes over all the characteristics of a Trojan virus. Though it cannot replicate like a worm virus it is also able to create new files by its own. It will release its own infective files all over the hard drives. In such ways there would be a large amount of files that computer users cannot delete easily. Because they are not sure if it is safe for them to remove those files fearing that what they do may cause harm to other programs. In fact, what those users consider are absolutely correct. The virus not only creates new documents by its own but also replaces or modifies files of other normal programs. If you are not sure what is the real files of the virus and remove the ones of other software it may be a problem. The related program will not work any more or it may cannot be opened at all. The Trojan disturbs computer system by placing its files into every corner on the whole hard drive thus the system can work improperly. As a significant symptom, the speed of the infected machine will be greatly slowed down. And there will be random error codes when the machine is running.
The reason why a computer is hacked by Win32/bitcoinminer.AF is hard to tell. Nowadays, computer has become an obbligato instrument in our daily life and the internet makes the world smaller and much more interesting. However, when we are enjoying the convenience the internet brings to us we are also frustrating the bad effects it causes. There are not only knowledge spread online but also some infectious factors. When we are visiting some web pages there could also be items on the page that have been modified or replaced by Cyber criminals with some infectious factors. Thus as soon as we click on those items the infectious files will get chance to invade into our computers. Another possible way is that we download and install a program from online resource, but if the original package has been ever changed we may install viruses at the same time when we install the software. This Trojan virus is spread in those common ways. And after it settles down to a target computer there are more and more weird symptoms pops up on the unlucky machine. For example, computer users feels bad when they are trying to open a new tab on the browser or trying to run some programs you may realize that it takes more time for you to do that. Sometimes you may get different error codes when you start up the infected computer. And there stays the infection alert but you cannot remove the Trojan virus your antivirus detects.
The Trojan virus can bemuse computer users on its existence by modifying itself as part of regular and safe files of some programs. It enters a target computer without the consent of computer owners conquering the whole computer system in secret way. How ironic it is when all its tricks are done under the eye of the users. Besides, the Trojan can also escape from the scan of antivirus programs. That is why many computers are infected when there are antivirus software on them.
Note: Manual Removal requires expertise and it is for advanced users, if you don’t have much experience in dealing with this Trojan virus. Contact YooSecurity Online PC Experts for removal assistance.

Symptoms of Similar Trojan Infection :
– This virus can escape from most antivirus protection and get itself installed on computers especially with Windows operating systems.
– It can cause constant stuck or even blue screens on the infected computers.
– Computer users will experience constant security pop ups on the computers which may not truly represent the status of the PCs.
– Certain malware or spyware may be prompted by these fake security pop ups which will end up scamming money.
– Sensitive data like privacy can also be stolen and taken advantages by cyber criminals.
Manually Remove Win32/bitcoinminer.AF Step by Step
Up till now, there is not a perfect antivirus that can detect this pesky Win32/bitcoinminer.AF virus or delete it completely. It has been updated by remote and backstage cyber criminals and is able to escape from the scan of any anti-virus programs thus it is hard to be removed or even found. The most effective way is to remove it manually. The following instructions need quite level of computer expertise. If you don’t know how to that correctly, please contact with YooSecurity online support now!
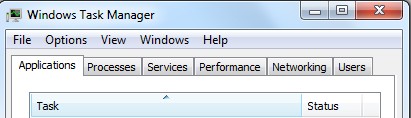
Step A: Open Windows Task Manager to end process related to this Trojan infection. To do that, press Ctrl+Alt+Del keys at the same time to pull up Window Task Manager; go to Processes tab on top and scroll down the list to find.
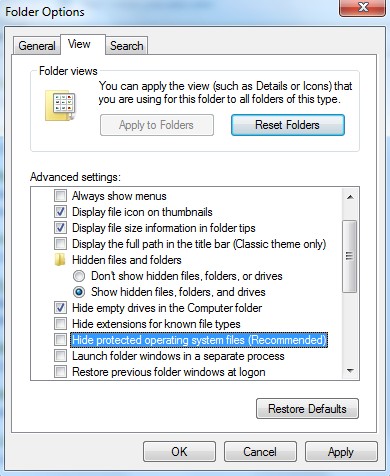
Step B: Open Control Panel from Start menu and search for Folder Options. Go to Folder Options window, under View tab, tick Show hidden files and folders and non-tick Hide protected operating system files (Recommended) and then click OK.
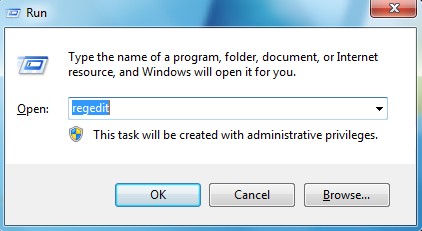
Step C: Press Windows+R keys to pull up Run box and type in regedit to open Registry Editor.
Step D: Delete all these associated files and registry entries with this Trojan virus from Registry Editor. The registry files are listed randomly. Besides, you need to delete the infection files of the redirect virus from your system files to prevent it from coming back. Those files are named randomly also but may be different on different operating systems.
Video on How to Modify or Change Windows Registry Safely:
Conclusion and Tips:
Win32/bitcoinminer.AF is a new threat to computers categorized to Trojan infection field. It can be got when you are redirected to some new or unsafe links. This Trojan can also be bundled with some regular programs and installed to the target computer along with the installation of the software. Trojan virus are designed to steal computer user’s personal database by Cyber criminals and this one is one of them. It is enabled to access your documents on the hard drives and will be able to change default settings. Antivirus may not even scan it out sometimes. Because this virus can escape from the scan by disguising as part of a legal program file. However,since the amount of infection files are increasing the virus cannot hide successfully any more. Antivirus can seek out its existence and give you the warning that your computer has been infected by this virus. But it may be too late. To protect our computer you had better give it a full scam regularly to see if there are any potential risks on it. And do not download or accept remote files from unknown ends. As soon as you find there is infection on your computer you should ask some people who are computer savvy or experts to help you remove them completely. Do not take complicated operations if you don’t know much about computer.
Note: Have tried many methods but failed to get rid of this Trojan virus? If you have no clue, please contact YooSecurity Online Experts in time to save your computer.
Published by Tony Shepherd & last updated on November 14, 2013 1:11 pm










Leave a Reply
You must be logged in to post a comment.