Why am I getting a pop up from a Trojan Horse Patched_c.NEE virus? My computer has always been protected by antivirus. How can this Trojan virus slip into the system? Are there any other viruses coming together with this Trojan? What can they do to my computer? How do I check and remove this Trojan virus and all the other potential threats?
Trojan Horse Patched_c.NEE Virus Description
Trojan Horse Patched_c.NEE is a Trojan virus alert that can pop up on computers that have been attacked by this infection. Due to the stubborn and aggressive characters of this virus, it has managed to escape from many antivirus protection tools and sneak into the targeting computers without consent. Usually, a Trojan virus like this Trojan Patched_c.NEE can come from different places especially from the internet. Taking advantages of the internet, it can be spread worldwide and attack computers from different areas. Hiding and disguising itself among many fishy web sites and shady programs, it won’t be noticed at first until it starts to create all kind of chaos on the infected machines or is detected by PC protection programs.
Trojan viruses are usually created in groups or families. They can be named differently according to the alphabet or Arabic numerals. But they all share the common characters. Similar to Trojan:JS/Medfos.B virus, Trojan Horse Patched_c.NEE virus can also collect valuable private information out of the infected computers and sell them to third parties. This is the most obnoxious character of this kind of Trojan. Other than that, this Trojan infection shares the characters of 1) installing itself without consent; 2) escaping from many antivirus programs; 3) bringing constant pop ups and 4) helping other viruses get in. All in all, computers will suffer from many consequences when being attacked by this Trojan infection. If the virus cannot be removed in time, computers will be caught among other troubles including stop functioning properly.
To save your computer and prevent private info from being stolen, please remove this stubborn Trojan Horse Patched_c.NEE virus off the computer. Contact YooSecurity Online PC Experts if you are not able to do that by yourself.

Steps on How to Remove Trojan Patched_c.NEE
Many Trojan infections can escape from antivirus programs nowadays. It’s either the antivirus programs have expired or the viruses are associating with unfriendly third parties that makes them able to install without permission. Hence, to remove this Trojan Horse Patched_c.NEE virus, getting another virus remover may not help much. And since this Trojan virus can scatter its associating items in different locations, a complete removal is important. Below are some manual removal steps on how to remove this Trojan virus. To remove this virus manually, expertise is required:
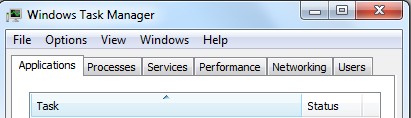
Step 1: Open Windows Task Manager to end processed related to this Trojan Patched_c.NEE threat. To do that, press Ctrl+Alt+Del keys at the same time or right click on bottom Task Bar and select Start Task Manager.
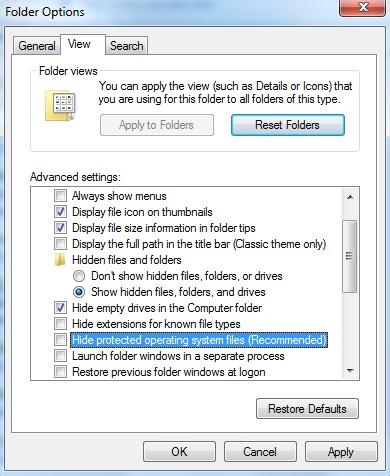
Step 2: Open Control Panel from Start menu. Go to Folder Options and under View tab, select Show hidden files and folders and non-select Hide protected operating system files (Recommended) then click OK.
Step 3: Go to Registry Editor. First press Windows+R keys and then type regedit in Run box to search. Delete registry entries associated with this Trojan Horse Patched_c.NEE infection:
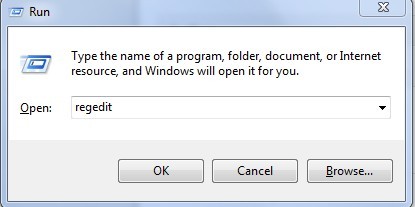
%AllUsersProfile%\random.exe
%AppData%\Roaming\Microsoft\Windows\Templates\random.exe
C:\Windows\System32\services.exe
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunRegedit
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableRegedit”
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\{rnd}=disable
Video on How to Modify or Change Windows Registry
Conclusion
Trojan Horse Patched_c.NEE virus is definitely not the first Trojan virus that can escape from antivirus programs. Computer hackers will be able to benefit from this kind of Trojan virus because they can control it and make it able to access private info on the infected computers. Computer users may not even notice when their private data is stolen. Trojan Horse Patched_c.MIS virus comes from the same group with this Trojan Patched_c.NEE. Not only your personal info will be in risks of being stolen, the system can encounter many troubles and come through a hard time of operating. For instance, programs can stop responding often whenever you try to run them. Internet connection can also be cut off frequently making you impossible to surf online properly. The longer this Trojan infection gets to stay in your computer, the more damage it can create and the more computer hackers can benefit.
Note: If you still find it hard to achieve a complete removal of this Trojan virus, please contact Online PC Experts now to get help from professionals and to save the computer ASAP.
Published by Tony Shepherd & last updated on May 23, 2013 2:19 am










Leave a Reply
You must be logged in to post a comment.