How do I get rid of this Trojan Horse Generic35.KER pop up on my laptop? It keeps being detected by Malwarebytes. But each time I try to delete the infections, software becomes unresponsive. When I get to run another security check, I receive similar Trojan pop ups again. I’m worried that someone can hack my laptop and mess things around. The laptop is used for business and is very important to me. How can I go about deleting this Trojan virus?
Trojan Horse Generic35.KER Virus – Remove Trojan Infection
Trojan Horse Generic35.KER is a Trojan process that can hide deep down into a computer system and wait for its chances to help hackers steal important data or even win over control of the machine to conduct all kinds of possible damage. It belongs to one kind of malicious code. Trojan horse is the full name of this group of computer virus coming from Greek myths. A Trojan horse infection is very common today especially with the increasing numbers of computers each year. Any computers could have the chances to be attacked by this type of computer threat even when there’s antivirus protection installed.
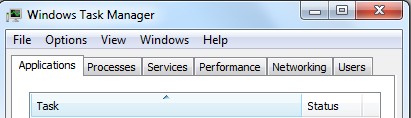
Trojan Horse Generic35.KER virus is another member from the Trojan Generic family. Unlike regular computer viruses, this Trojan horse won’t duplicate itself when installed on a system. But it can self-recover once being found and deleted by users as it usually comes with backups inside the system. Basically, victims of this Trojan infection cannot locate the virus easily as it’s a master in keeping its processes under all sorts of disguises. It can pretend to be system files by simply renaming its applications with confusing words and letters like “0” and “O” which are hard to tell the differences visibly. The Trojan horse can also cover itself deep inside the infected system from being seen easily. That is why victims usually get higher CPU usage percentage and yet there aren’t too many processes to be found in Task Manager. Compromised computers are often slow in running as the Trojan virus has taken up lots of CPU resources. It certainly has created a suitable environment for remote hackers to do what they want and steal valuable data out of the infected machines.
Since a Trojan horse is able to hide from PC protection tools and disguise itself as system files, to completely get rid of Trojan Horse Generic35.KER virus, manual removal process is believed to be efficient. One will need to deal with lots of system files and registry entries and distinguish the Trojan files from system data so as to accomplish a complete clean. Hence, expertise will be needed during the removal processes.
Note: To completely get rid of this Trojan horse generic infection, contact YooSecurity Online PC Experts to get help if you are not a computer literate:

A Sum-up of Trojan Virus Characters & Effects
1. Trojan Horse Generic35.KER can be installed by tricking computer users into downloading certain types of fake executable applications online.
2. Upon install, it can set itself as the startup process of the system so that it can be automatically launched each time the affected PC starts.
3. It can hide its processes inside the system via various ways including pretending to be system files under different locations.
4. It can take up lots of CPU resources and cause constant stuck on the PC making it impossible for users to operate.
5. Most importantly, the Trojan horse is there to open backdoors for remote hackers to collect valuable information from the system or even let them take over control of the machine.
6. A system infected by this Trojan will become vulnerable which will easily provide chances for other malware to sneak inside.
A Step-by-Step Trojan Manual Removal Guide
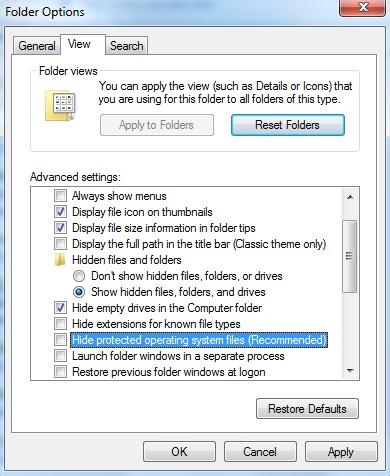
Step 1: Open Control Panel from Start menu. Go to Folder Options and under View tab, select Show hidden files and folders and non-select Hide protected operating system files (Recommended) then click OK.
Step 2: Open Windows Task Manager to end processed related to Trojan Horse Generic35.KER virus. To do that, press Ctrl+Alt+Del keys at the same time or right click on bottom Task Bar and select Start Task Manager.
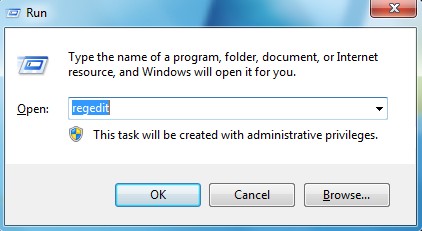
Step 3: Go to Registry Editor. First press Windows+R keys and then type regedit in Run box to search. Delete registry values associated with this Trojan infection.
Similar Video on How to Modify or Change Windows Registry:
Conclusion
This Trojan Horse Generic35.KER virus is nasty enough to escape from lots of antivirus protection tools and manual removals. Usually, this type of Trojan infection pretends as trustworthy applications to trick average PC users into downloading the programs on their own without knowing the existence of the infection. It can also be bundled with unauthorized freeware online to sneak into the targeted computers. This piece of Trojan horse is a master in hiding itself in the infected system. The longer it gets to stay inside the PC, the more it can help remote hackers benefit from valuable data collected from the infected system. It’s like the key to your computer. When the door is open, remote hackers get to do or steal what are valuable to them; system will become vulnerable at the same time because of this infection which will give chances for other dangerous computer threats. If an instant clean cannot be achieved in time, owners of the affected PCs will face a lot more problems. Due to its specific characters, manual removal with expertise is the most effective way to take out this Trojan horse generic35.ker. Any mistakes during the process can cause severe system problems.
Note: Cannot identify the Trojan files and processes inside the system? Have tried different things without success? Contact YooSecurity Online PC Experts now to get further assistance now:
Published by Tony Shepherd & last updated on November 21, 2013 12:15 pm










Leave a Reply
You must be logged in to post a comment.