Does antivirus software detect a Trojan virus in your computer? Are you getting an alert saying Trojan Horse Generic29.AJGE virus is risking the system? Is this Trojan virus associating with computer hackers? Do we need to worry about our private info? How do people remove this annoying Trojan completely?
Trojan Horse Generic29.AJGE Virus Description
Trojan Horse Generic29.AJGE is categorized as a Trojan infection which comes from a large family of Trojan. Trojan Horse Generic29.AHHS is another member from this family that has been attacking computers all around the world lately. Trojans are usually put online into many hacked sites or unknown free programs. Whenever computer users visit these sites online or download these unfriendly programs, Generic29.AJGE can come into the systems together. Hence, computers from all around the world that are connected to the internet and available to land on these web sites can be targeted by this Trojan infection. Computers won’t be able to take the risks caused by this Trojan virus even though they are protected by antivirus applications.
Do not underestimate a Trojan virus as it can bring unpredictable consequences on the compromised computers. Even though it’s a small piece of virus, Trojan Horse Generic29.AJGE virus can be as nasty and dangerous as malware and ransomware. But unlike malicious programs which can be seen visibly, this Trojan virus does not show up in the form of an object or software. It’s very active in backstage activities and may allow the associating malware to get in the infected system when the time is right. By that time, you could face more than one problem on your computer. This Trojan virus can create all kinds of pop-up alerts as well to annoy computer users and threaten them into believing their PCs are gone bad and they need to purchase something to recover the systems. These could all be the scams brought up by this Trojan virus in your computer. But most important, this Generic29.AJGE virus is put into computers in order to help computer hackers benefit from its victims’ private info. In other words, one should be worrying that personal data may be stolen by this Trojan virus. Hence, it should be removed soon.
Have no idea on how to remove this Trojan Horse Generic29.AJGE but don’t want computer to go bad? Contact YooSecurity Online PC Experts now to save your computer from all the consequences brought up by this Trojan virus that you are about to experience.

Consequences Caused by Generic29.ajge Virus
1. Trojan Horse Generic29.AJGE is put on computers to help PC hackers benefit from its victims’ private information;
2. Associating malware or ransomware will be brought into the computer as well to extend the damage;
3. Security alerts may keep popping up to interrupt your movements on the computer;
4. Certain functions of the infected computer can be disabled by this Trojan virus including the internet connection;
5. System crash down could be caused once the infection has gone bad.
Steps on How to Remove TrojanHorse Generic29.AJGE
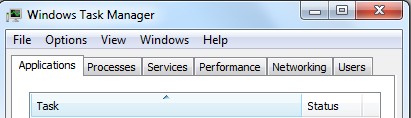
Step 1: Open Windows Task Manager to end processed related to [Trojan Horse Generic29.AJGE]. To do that, press Ctrl+Alt+Del keys at the same time or right click on bottom Task Bar and select Start Task Manager.
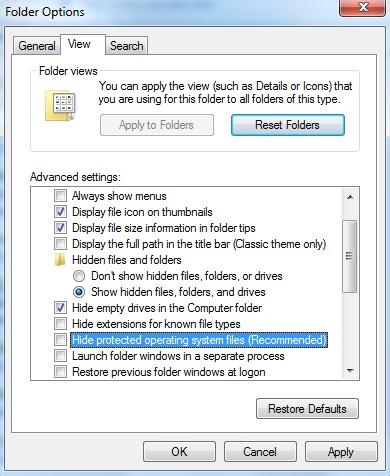
Step 2: Open Control Panel from Start menu. Go to Folder Options and under View tab, select Show hidden files and folders and non-select Hide protected operating system files (Recommended) then click OK.
Step 3: Go to Registry Editor. First press Windows+R keys and then type regedit in Run box to search. Delete registry entries associated with this Trojan infection:
%Windows%\system32\[rnd].
%AllUsersProfile%\Application Data\[tmp]
C:\windows\system32\services.exe\””
C:\Windows\winsxs\amd64_microsoft-windows-none_2b54b20ee6fa07b1\””
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunRegedit
HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\System “DisableRegedit”
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\{rnd}=disable
Video on How to Modify or Change Windows Registry
Conclusion
Trojan Horse Generic29.AJGE virus can escape from many antivirus applications and sneak into computers from different locations without permission from PC owners. It can hide under hacked web sites or within free software. Once computer users visit these sites or install these unfriendly programs, they somehow will allow the install of this nasty Trojan virus. Once it’s successfully got in, this Trojan infection will start by changing the structures or default settings for its own good. It will be able to steadily stay in the infected machine to bring constant chaos. Private info on the infected computer is the most important target of this Trojan virus. Remote PC hackers can benefit from them later on. Hence, it’s better to get rid of this Trojan infection before more damage happens.
Note: Cannot get rid of this Trojan Horse Generic29.AJGE virus successfully? Contact Online PC Experts now to save your computer from suffering and to protect your privacy from being stolen.
Published by Tony Shepherd & last updated on May 10, 2013 4:33 am










Leave a Reply
You must be logged in to post a comment.