Need help of fixing a problem on my computer. I have XP as my system, yesterday, after I downloaded a problem and installed it to my computer, I got a virus called Backdoor.bot.MSIL. I tried to get rid of this virus by uninstalling the program which brings it to my system, but it didn’t work. I still got the virus warning from my security tool, why can’t my security tool remove it for me but only inform me? What should I do?
Brief Introduction to This Trojan
Backdoor.bot.MSIL is classified as a Trojan horse infection that designed by cyber criminals. It is a newly spread infection on the Internet. Users can get attacked by this virus with many ways. It is hard for PC users to prevent it from coming as it can infiltrate target computers on the background without being known by computer users. Even though users can install anti-virus programs to protect their machines, but this infection can bypass the security tools and mess up the systems. Also, after it comes to the target computers, it can disable the security system which can make the infected machine be totally compromised, which mean the infected system can be attacked by more viruses from the web.
This Backdoor.bot.MSIL Trojan virus can be widely spread on the web as hackers can put it into many pages. Cyber hackers can take control of pages that have already been hacked and implant this Trojan to the server, so that when the innocent users come to visit the corrupted websites, their visiting machines can be forced to download this Trojan automatically and instantly. It is not easy for users to notice that as all activities of it are performed on the background. If a computer is infected with this virus, other computers share the same network can be targeted as well.
When this Backdoor.bot.MSIL invades the target computers, the machines can get poor performance as this Trojan can mess up the whole system from many aspects. This Trojan can make changes to the system registry so that it can be activated from the startup when people boot up the infected computers. With wrong settings, the machines will suffer from constant problems like black screen and blue screen of death with no reason. What’s worse, cyber hackers can be able to utilize this infection to connect to the target computers, so that they can do more bad things to the infected machines. Privacy like bank password and credit card information can be the main targets for those bad crooks to steal as they can use the information to get illegal benefits.
Some Traits about This Trojan
-Can slow down the performance of the computer, or even blue screen.
-Can create many junk files which occupy a lot of space in hard drive
-Can download other malicious programs into computer, which make further damage.
-Your sensitive information can be stolen by hacker who can access to your computer with the help of this Trojan.
-Cay give you many redirects all the time no matter what you are doing.
-May pretend as an anti-virus program and cheat you that computer is in dangerous, and ask you to pay to remove the threats.
NOTE: If you find any of these symptoms on your computer, that proves your PC is under attack and seriously infected. If you are not a computer savvy, Please contact YooSecurity Online PC Experts to remove this Backdoor.bot.MSIL for you.
Manual Removal Guide of Trojan (For Computer Literate)
There is a removal guide of Trojan provided here; however, expertise is required during the process of removal, please make sure you are capable to do it by yourself.
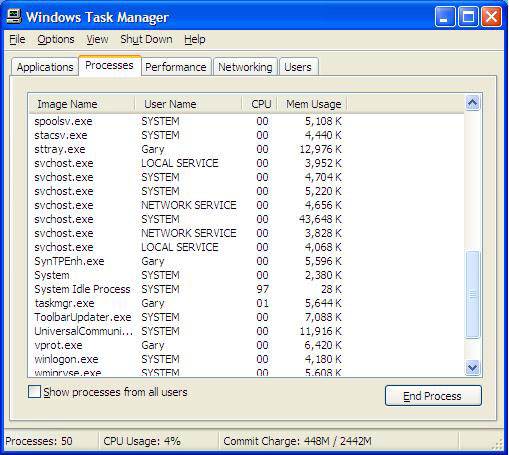
Step 1: Find Ctrl, Alt, and Delete these 3 keys and then press them together to open task manager to end the process related to this Trojan, the name of the process of it is random.
Step 2: Try to find Folder Options in Control Panel, select the View tab, and then tick Show hidden files and folders and non-tick Hide protected operating system files (Recommended) and then click OK.

Step 3: Try to find the files which relate to this Trojan, and delete them all.
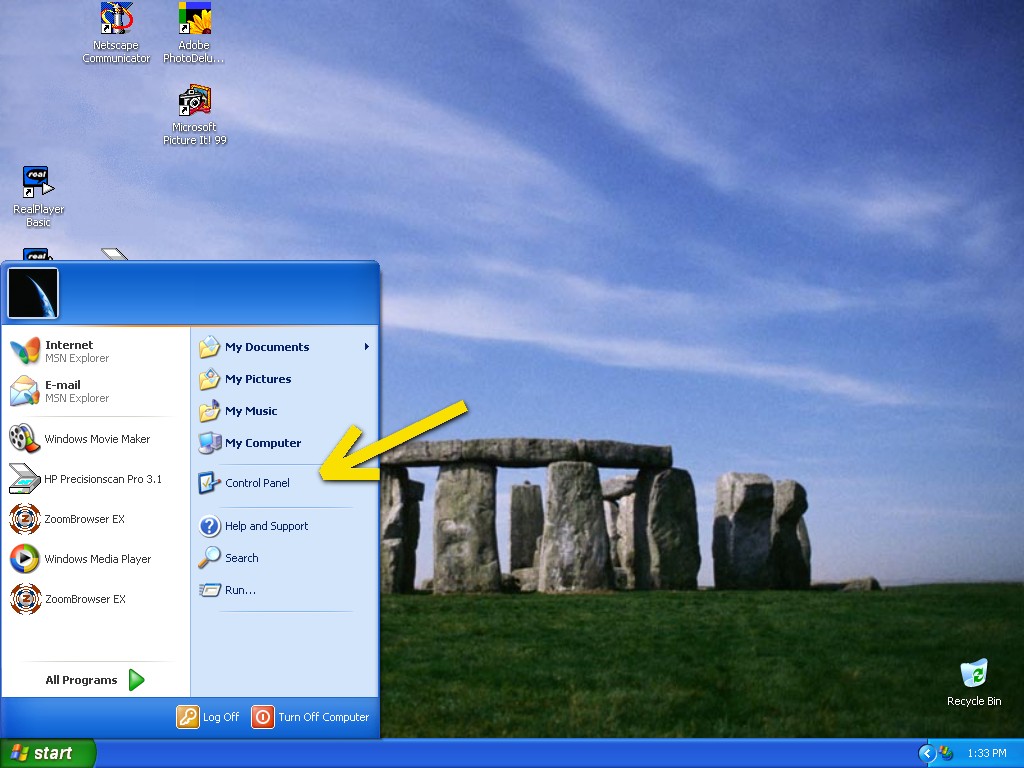
Step 4: Click on Start button at the right lower corner, then click on Control Panel
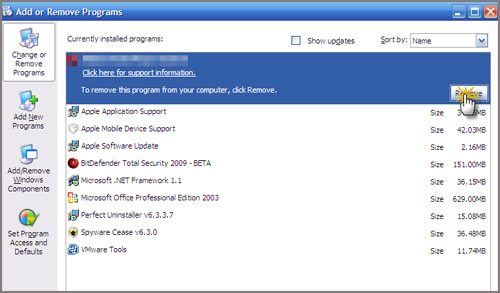
Then you will come to the Control Panel windows, click on Add and Remove Programs
![]()
Then try to find the program which relates to this Trojan, highlight it and choose Remove, the program’s name is random.
Step 5: Click on Start button or press Win+R, then type regedit in the box to open Registry Editor, after that, try to find
C:\Users\profile name here\AppData\
HKCU\Software\Microsoft\Windows\CurrentVersion\Run
Similar video guide to modify Windows registry:
Conclusion
Backdoor.bot.MSIL can be spread by the people who have evil purposes on the Internet. It can be capable to damage the security system, so that it can help more computer infection to invade and make more troubles. Cyber criminals who make this infection can use it to establish illegal connection to infected computers. In this case, personal information saved on them can be leaked out to those bad people. That can make the users suffer from financial losses. So, to avoid the bad things happen, people must remove this infection in time if they get this infection on their computers.
Suggestion: To follow removal guide that mentioned above, a level of computer knowledge is needed. Still can’t get out of Backdoor.bot.MSIL? Contact online experts for help now!
Published by Tony Shepherd & last updated on August 26, 2015 1:09 pm











Leave a Reply
You must be logged in to post a comment.