The Chinese censorship authorities will block any site which they deem to contain material detrimental (even tangentially) to the Chinese Communist Party. The way they do this is by blocking at the IP address level. A crude tool indeed. Most websites in the world are hosted on Shared Hosting Accounts so if an IP address gets red flagged it could potentially impact hundreds of other sites hosted on the same server, using the same IP address. To create an analogy, it’s a bit like living in a shared house and one of the members is caught for being involved in illicit activities.
Among blocked sites are such popular sites as Google services (including Gmail, Google maps, Google docs and others) YouTube, Facebook, Twitter, Wikipedia, VOIP services like Skype and Snapchat and tones of others popular resources. So if you are going to China, you need to care about your Internet freedom in advance. Access the blocked Site in China on your Mac, you can setup vpn connection on your device using systems features. This is much more secure than using any additional application.
The Function of the Best VPN
VPN (Virtual Private Network) has become more and more popular as more and more workers work from home or travel on business. The best VPN service allows people connect their devices to their office network even if they are far away from their offices. If the workers who are on a business trip want to get company resources over the Internet, connecting to a VPN will really help. And you don’t need to worry about the security of your company resources because the resources don’t have to be uncovered directly on the Internet. In addition, when you connect to a VPN, browsing activity will be hided from your local network and ISP (Internet Service Provider). Consumers use a private VPN service, also known as a VPN tunnel, to protect their online activity and identity. By using an anonymous VPN service, a user’s Internet traffic and data remain encrypted, which prevents eavesdroppers from sniffing Internet activity. A VPN service is especially useful when accessing public Wi-Fi hotspots because the public wireless services might not be secure. In addition to public Wi-Fi security, a private VPN service also provides consumers with uncensored Internet access and can help prevent data theft and unblock websites.
The Best VPN Service boils down to what kind of user you are and what you are trying to achieve. There is a much larger group of people who want to improve their anonymity but don’t need to take this to forensic depths, for example BitTorrent users and normal citizens living under repressive regimes. Furthermore, when you are traveling, you also can connect your devices like laptop, tablet even phone to your own home Network. After you set up your own VPN and connect to it, you will has the ability to get into a Windows Remote Desktop over the Internet, use your local files shares and even play games over the Internet seems you were on the same local area network. Connecting to a VPN is such beneficial. It is a wise choice to connect to a VPN rather than ask colleagues or friends to help you get what you need.
Suggestion: If you don’t know how to access Blocked Site on Mac in China, you’re welcome to contact Our online technical team by clicking Start Live button bellow:

Is using VPN safe?
“While using VPN service, I am worried about my personal information security.
Is it possible that my personal information can be catches by some technical methods during the time I am using VPN? If it can be done, how does it work?”
VPN is used for security reasons. This is a perfect solution to keep your personal data protected. Your traffic and all your data is encrypted inside vpn tunnel. VPN safety is based on tunnelling protocols and encryption techniques.
The VPN security model provides:
• Confidentiality such that even if the network traffic is sniffed at the packet level (see network sniffer and Deep packet inspection), an attacker would only see encrypted data
• Sender authentication to prevent unauthorized users from accessing the VPN
• Message integrity to detect any instances of tampering with transmitted messages
Not all VPN service providers are worth your trust. Some diligently log your connection times, dates, IP addresses, keep track of how long you’re connected, and some even keep an eye on the types of traffic that you send through their networks while you’re logged in. They’ll tell you it’s in order to make sure you’re not doing anything illegal, or anything that would damage their network, but that level of snooping does kind of go against the whole purpose of a VPN. Some virtual networks may not use encryption to protect the privacy of data. While VPNs often provide security, an unencrypted overlay network does not neatly fit within the secure or trusted categorization. So selecting a reliable vpn service provider pay attention if they provide encryption.
Guides to set up VPN on Mac
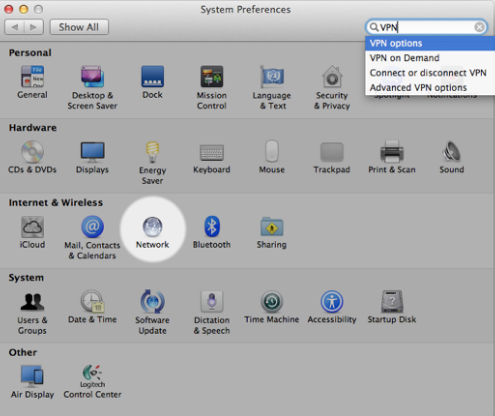
1. Open System Preferences > Network.
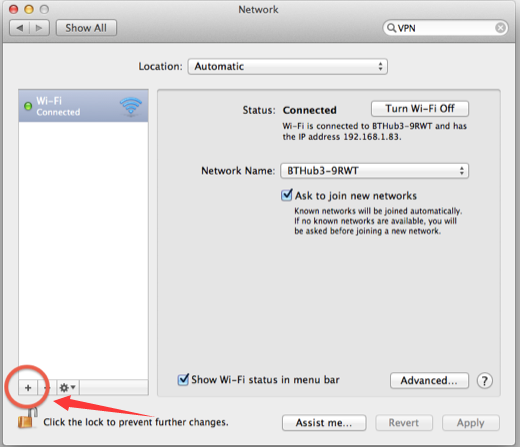
2. Click the + sign.
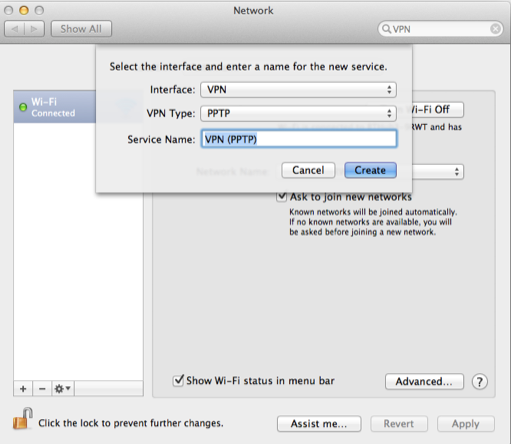
3. Select VPN, then pick L2TP or PPTP.
4. Enter in your server address and account name, then click Authentication Settings.
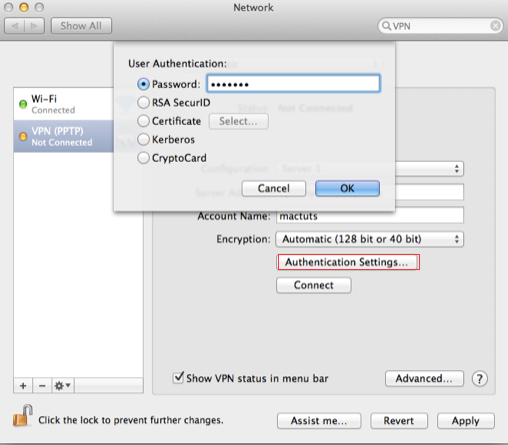
5. Enter in your password and shared secret, then click Ok.
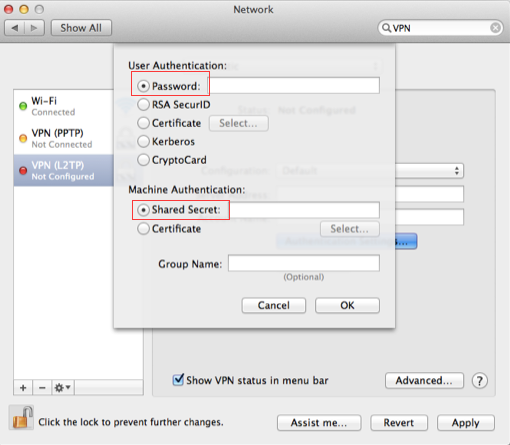
6. Click Connect.
Video Shows How to Open Blocked Site on Mac in China
If someone follows the entire information, then they can easily access Hulu sitting anywhere in China. But make sure that you are choosing the right VPN service provider and not fall into the hands of wrong providers. When installed and connected a VPN creates a separate and encrypted tunnel for your internet data traffic. Whatever you do online is transferred through this secure and encrypted tunnel away from the eyes of snoopers and hackers, however your Internet Service Provider (ISP) can see you are connected to a VPN but can not see what you are doing as your internet data traffic is hidden by VPN Encryption. Using a VPN is absolutely legal, unless you don’t use to for any criminal activities. There are misuses of every technology.
Warm prompt: If you don’t know which VPN service is the best for you or how to set up VPN on Mac, computer, laptop, android smartphone, tablet, or iPhone &ipad device, you’re recommended to live chat with Our Online Expert for instant help! We will take care everything for you!
Published by Tony Shepherd & last updated on January 16, 2018 2:10 am











Leave a Reply
You must be logged in to post a comment.