This morning Norton started repeatedly detecting both Trojan.gen.2 and Trojan.zeroaccess.b. I ran Norton’s zeroaccess removal tool and the power eraser as instructed on the Symantec site. Neither helped. Hoping I can get some additional help here…everything is running extremely slow and “just in time debugging” keeps popping up. What will you do if you have the same problem?
What is Trojan.Zeroaccess.2
Trojan.Zeroaccess.2 is notorious for its destructive power. Once your computer has been infected by such Trojan virus, your computer will be impacted heavily even the system will be destroyed completely. Adopting the usual method by making a backdoor program installed in your computer. This virus can easily gain the authority to have its full swing. This virus is very small so it’s easy for Trojan.Zeroaccess.2 Virus spreading widely. It’s a parasite on sites, links, files and some computer devices. Accidentally, you will touch the infected links, sites or files, Trojan.Zeroaccess.2 will grasp this chance to access into your computer. To invade your computer, the first thing it has to do is to take your antivirus into camp. This is also the key step for it to obtain more authority to control your computer. After that, it has successfully infected your computer.The virus is not attacking your computer alone. After it successfully gets into your computer, it will import more and more other even more superior and vicious virus or malware to launch more destructive attacking to your computer. Its tremendous destructive power and concealment that almost no antivirus can detect it. Even if the antivirus has detected it, it can’t be removed by the antivirus whatever effort you try. The second feature is its persistent and continually enhancing it’s power of damage to your computer. From the time you get caught by such virus, Trojan.Zeroaccess.2 Virus keeps bringing in lots of other unaware malware or virus. These virus are even more fierce than Trojan.Zeroaccess.2 virus itself. They exhaust all RAM and CPU room which will make your computer more and more slow. In this situation, you will find that even if you just open one or two programs. The RAM and CPU are almost occupied 100%. What’s worse, it seems you computer system always occurs error here and there. The last feature you may never notice is that you may be exposed to hijackers who release those virus to your computer. That is to say, your personal information will be revealed to them and it will lead to casualty or property loss. Hurry up to get Trojan.Zeroaccess.2 off from your computer!
To make your computer healthy, Live Chat with YooSecurity Experts Now, or you can follow the manual removal guide below to get your problem fixed. (For advanced computer users)

Key sentences to judge if your computer has been infected Trojan.Zeroaccess Virus
A. Your computer is something not normal as usual such as running very slowly.
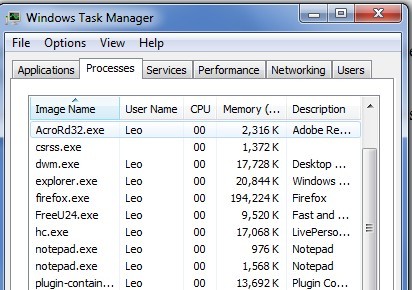
B. When you open the Task Manager, you can find some strange progress which you never found before.
C. Some of your computer functions are unavailable or some normal legal program can’t run or there are unusual conditions of them.
D. It always constantly happens that your system has errors somewhere.
E. Lately, your computer system will be totally destroyed.
Best Way to Remove Trojan.Sirefef.GZ & Manual Removal Step by Step?
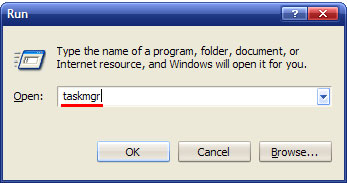
Step 1: Press CTRL+ALT+DEL or CTRL+SHIFT+ESC. Open the Windows Task Manager.
If that didn’t work, try another way. Press the Start button and click on the Run option. This will start the Run tool. Type in taskmgr and press OK. This should start the Windows Task Manager
Step 2: Within the Windows Task Manager click on the Processes tab. Find the process by name. random.exe. Then scroll the list to find required process. Select it with your mouse or keyboard and click on the End Process button. This will kill the process.
Step 3: Delete malicious registry entries.
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Active Setup\Installed Components\random
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\run\ Trojan.Zeroaccess.2
Step 4?Remove malicious files of Trojan.Zeroaccess.2
C:\WINDOWS\assembly\GAC\Desktop.ini
C:\WINDOWS\system32\ping.exe
Video of Key Steps on How to Modify or Change Windows Registry:
Based on various situations and computer skills, you can choose the following solutions fit for you.
1. Follow the steps we provide to manually remove the virus.
2. If you failed to remove Trojan.Zeroaccess.2Virus Infection with the method above, please consult YooSecurity certified professionals to remove it completely. Live chat with professionals now
Published by Tony Shepherd & last updated on November 19, 2012 9:02 am










Leave a Reply
You must be logged in to post a comment.